-
Content Count
519 -
Donations
$0.00 -
Joined
-
Last visited
-
Days Won
18
Posts posted by CyberAbc
-
-
Welcome to our family.
Enjoy!
-
Welcome to our family.
Enjoy!
-
Welcome to our family.
Enjoy!
-
Welcome to our family.
Enjoy!
-
Welcome to our family.
Follow the rules.
-
Welcome to our family.
Follow the rules.
Enjoy!
-
welcome to our family.
Follow the rules.
Please feel free to talk us any time if you need....
Enjoy!
-
welcome to our family.
Follow the rules.
Please feel free to talk us any time if you need....
Enjoy!
-
welcome to our family.
Follow the rules.
Please feel free to talk us any time if you need....
Enjoy!
-
welcome to our family.
Follow the rules.
Please feel free to talk us any time if you need....
Enjoy!
-
welcome to our family.
Follow the rules.
Please feel free to talk us any time if you need....
Enjoy!
-
welcome to our family.
Follow the rules.
Please feel free to talk us any time if you need....
Enjoy!
-
welcome to our family.
Follow the rules.
Please feel free to talk us any time if you need....
Enjoy!
-
welcome to our family.
Follow the rules.
Please feel free to talk us any time if you need....
Enjoy!
-
welcome to our family.
Follow the rules.
Please feel free to talk us any time if you need....
Enjoy!
-
welcome to our family.
Follow the rules.
Please feel free to talk us any time if you need....
Enjoy!
-
 1
1
-
-
welcome to our family.
Follow the rules.
Please feel free to talk us any time if you need....
Enjoy!
-
welcome to our family.
Follow the rules.
Please feel free to talk us any time if you need....
Enjoy!
-
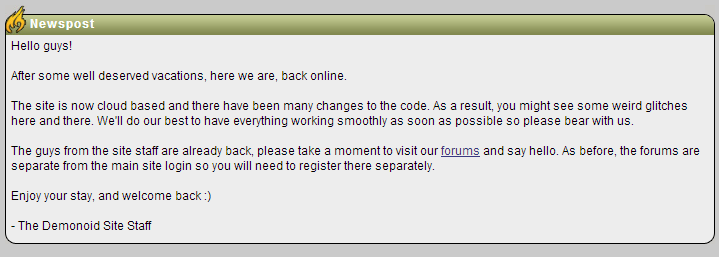
After 20 months of downtime the infamous Demonoid BitTorrent tracker has made a comeback. The tracker returned a few weeks ago, but the now the website is accessible again too. Former users are still able to use their login details, and most of the old torrents are still listed on the site.

As the single largest semi-private BitTorrent tracker that ever existed, Demonoid offered a home to millions of file-sharers.
This changed abruptly August last year when a series of troubling events took the site offline. When it was still down after a year, many gave up hope that it would ever return.
Today, however, the site appears to have made a glorious comeback on Demonoid.ph, which the .com and .me domains are also linked to. TorrentFreak contacted the team behind the resurrection who confirmed the relaunch.
“We are running a pre-launch today,” TF was told by the admin, who added that the site could go offline again for a while if something breaks.
A message posted on the site’s homepage explains that Demonoid made some changes to the backend, and that there may be some glitches. However, several Demonoid users confirm that they are able to login using their old credentials.
“The site is now cloud based and there have been many changes to the code. As a result, you might see some weird glitches here and there. We’ll do our best to have everything working smoothly as soon as possible so please bear with us,” the Demonoid team writes.
Demonoid comebackThe above is good news for those who hold Demonoid dear. Several of the former staffers are still involved according to the announcement, but for now it’s unclear whether the site’s management is still in the same hands as before.
However, the current resurrection is linked to the old domains, which suggests that it’s indeed the real thing.
Previously there were concerns that the user database may have been “compromised.” For example, last year a mysterious replacement surfaced, using a copy of the Demonoid user and torrent database. The operator of the spin-off claimed not to be related to the Demonoid owners, but he did have a copy of the site’s database.
Perhaps in the future the Demonoid team will be willing to explain a bit more about what happened over the past two years. For now, however, it appears that the comeback kid has pulled it off again.
-
 1
1
-
-
At its TechEd conference today, Microsoft announced the next step in its "mobile first, cloud first" strategy with a preview of Apache Cordova support in Visual Studio. Cordova is a toolkit for building apps for iOS, Android, and Windows using HTML, CSS, and JavaScript. With the Cordova integration, Visual Studio will directly support building apps for all of these platforms.
Visual Studio has previously supported third-party platforms when used with third-party products, such as Xamarin, which provides a .NET-based build environment for Android and iOS.
This time, the support is coming from Microsoft itself. The integration, now available as a preview release, includes templates both for regular JavaScript and Microsoft's JavaScript derivative TypeScript. Projects can be built, deployed, and debugged all from within Visual Studio, and this includes debugging on the Apache Ripple simulator, real devices (whether running Windows, Windows Phone, Android, or iOS), and the Android emulator.
The Cordova support is significant for a range of reasons. It fits with the company's newly promoted strategy of supporting its services on any platform, not just its own. Previously, the company shipped a range of toolkits for Android and iOS developers to make it easier for them to use Azure to provide back-end cloud services, but development for those platforms would still take place using those platforms' own tooling. This time, it's Microsoft's tools that will be used to develop for iOS and Android.
 Debugging a Cordova application within Visual Studio. This application uses the underscore.js library.Microsoft
Debugging a Cordova application within Visual Studio. This application uses the underscore.js library.MicrosoftThe Cordova support is also a little surprising because, for Metro-style Windows 8 and Windows Phone 8.1 applications, Microsoft has developed its own JavaScript, HTML, and CSS-based framework for use with WinRT. This framework could have been described as a Windows-specific take on the Cordova concept, and it was never entirely clear why Microsoft went that route rather than embracing the already established Cordova platform.
With Windows 8 and WinRT, everything old is new again.
Microsoft has other changes in store, too. In keeping with the more open Microsoft that was on show at Build earlier this year, the company is talking a bit about the future of the .NET platform.
Microsoft plans to develop a cloud-optimized version of .NET that's designed to be embedded into server applications. This will both slim down the framework, omitting features such as GUI support that aren't needed in server applications, and make it easier to distribute. Different applications on the same server will be able to integrate their own version of the framework, to make it easier to run different versions side-by-side. This is a capability that has been a feature of Java practically since its inception.
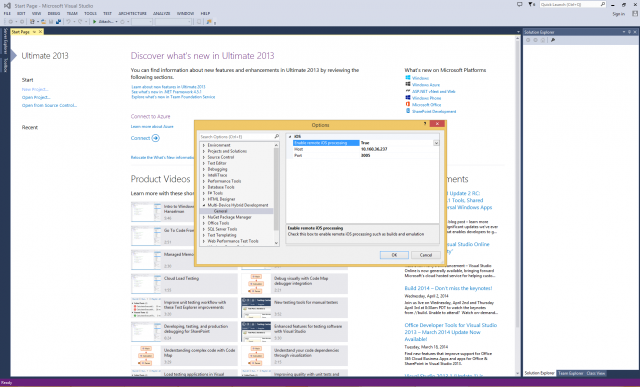 Building for iOS and running the iOS emulators is something that has to be done on actual Macs.Microsoft
Building for iOS and running the iOS emulators is something that has to be done on actual Macs.MicrosoftThe company also described some of the features of the next version of ASP.NET, its Web development framework. The next ASP.NET is going to be less monolithic and more modularized than the current framework, making it easier for developers to mix and match just the functionality that they need, for a simpler, leaner environment.
This development is all being done in coordination with the .NET Foundation that Microsoft also announced at Build. Redmond is actively collaborating with Xamarin to ensure that the new work is just as applicable to Mono on Unix as it is to .NET on Windows.
Partly cloudyThe company has also made some cloud-side announcements. Visual Studio Online, the cloud-based application lifecycle management platform built around Team Foundation Service, now has an API and set of hooks so that extensions and integration into third-party services can be developed.
An example of such an integration is integration into the UserVoice suggestion and feedback service. Suggestions made by end-users on UserVoice could be used to raise work items inside VSO, and progress on those work items could be reflected back in the UserVoice entry. Integrations with GitHub, Zendesk, and HipChat are all available or planned.
Companies wanting to move from an on-premises Team Foundation Server installation to VSO can now take advantage of a newly announced migration tool from OpsHub. The free program can copy data into the cloud while preserving change history, work items, and so forth.
Microsoft also announced a new feature for MSDN subscribers. MSDN subscribers will be able to use their subscriptions to run Windows 7 and 8.1 virtual machines in Azure to use them as test platforms.
-
David Helkowski stood waiting outside a restaurant in Towson, Maryland, fresh from a visit to the unemployment office. Recently let go from his computer consulting job after engaging in some “freelance hacking” of a client’s network, Helkowski was still insistent on one point: his hack, designed to draw attention to security flaws, had been a noble act.
The FBI had a slightly different take on what happened, raiding Helkowski’s home and seizing his gear. Helkowski described the event on reddit in a thread he titled, “IamA Hacker who was Raided by the FBI and Secret Service AMAA!” Recently Ars sat down with him, hoping to get a better understanding of how this whitehat entered a world of gray. Helkowski was willing to tell practically everything—even in the middle of an ongoing investigation.
Until recently, Helkowski worked for The Canton Group, a Baltimore-based computer consulting firm serving, among other clients, the University of Maryland. Helkowski’s job title at The Canton Group was “team lead of open source solutions,” but he began to shift his concerns toward security after identifying problems on a University of Maryland server.
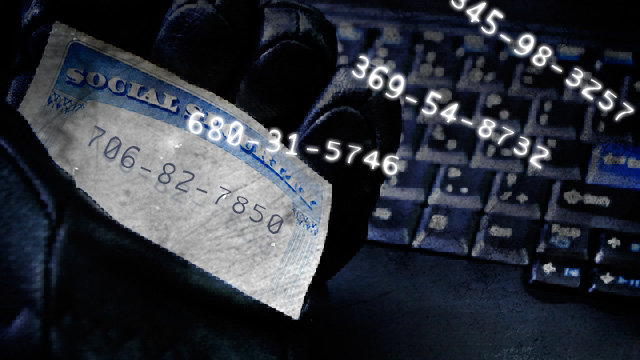
That transformation from developer to hacker came to a head when Helkowski decided that the vulnerabilities had gone unfixed for too long. He set out to prove a point about computer security both to the University of Maryland and to his employers. In early March 2014, working from a computer in his Parkville, Maryland home, Helkowski said that he exploited a misconfigured Web server and some poor database security in order to duplicate the results of a recent data breach that exposed the Social Security numbers and personal information for more than 300,000 current and former University of Maryland students and staff.
On March 14, Helkowski made his point rather dramatically by posting the university president’s Social Security number and phone number to reddit. He then sent an anonymous e-mail to the members of the university’s newly formed security task force, telling them in no uncertain terms just how horrible their security was.
Though he claims the message was not meant to sound threatening, it included lines like, “Out of politeness I’ll give you a chance to respond directly about this to me, and I’ll consider pulling it off the public Internet...Your internal IDs are listed below to get your attention.” If the security task force wouldn’t work with him, Helkowski told them to “consider this your fair warning and last contact from me.”
Despite his use of proxy and VPN services, the FBI began asking questions around Helkowski’s workplace the very next day. On the afternoon of March 16, agents investigating the case obtained a warrant. They kicked in the door of Helkowski’s home at 7pm that night. He was not arrested during the search, but his electronics were seized, his dog was (temporarily) lost, and federal charges may well be forthcoming.
The picture Helkowski painted of the circumstances leading up to his brush with law enforcement—and the still-present possibility that he will face criminal and civil charges—bears a strong resemblance to stories of information systems projects gone wrong at other universities and institutions. It has particular resonance for the public sector, where contractors can sometimes find it easier and safer to turn a blind eye to security problems rather than disclose them.
An unlikely hacker
Helkowski looks a bit older than his 32 years, with a slight build and a few gray hairs among the wiry black ones pulled back into his ponytail. He’s clearly confident in his abilities and confident that what he’s done is morally, if not legally, right. Helkowski told Ars he would act in exactly the same way if he had to do it all again.
An avid Steam gamer and anime fan, Helkowski is also a self-described computer keyboard aficionado. At one point, he had a collection of more than 35 keyboards, starting with a Northgate OmniKey that he picked up at a yard sale for $10. When the FBI raided his house, the agents had difficulty dealing with his current preferred keyboard—a Japanese keyboard with an English alphabet that he bought in the Akihabara district of Tokyo. The characters for each key are printed on the front of the key instead of its top, and its symbols don’t properly map to US standards.
“I figured out how to make it work with Windows by going in and making Windows Registry changes,” he told me. “But now I’ve just memorized which key maps to which symbol.”
Helkowski’s travels to Japan weren’t just driven by a desire for a clicky keyboard. Helkowski’s wife, a pianist and music teacher, is from Japan. He met her while she was in the US studying at Berklee College of Music. They dated but once. A few years later, after another relationship ended, he started communicating with her over the Internet again, finding she moved back to Japan to get a degree in music therapy. He traveled to see her, and they married six years ago.
“She teaches piano to kids 3 to 12 years old, and we have two grand pianos in our living room,” he said.
Helkowski has been a developer for a number of Maryland tech companies, doing everything from Web scripting to hardcore C development. Before joining The Canton Group last July, he worked as a contractor for a year at T. Rowe Price. But it was his experience in dealing with ColdFusion and doing data conversion work that greased the chain of events leading to the FBI.
(In what follows, all technical details were provided by Helkowski; neither the university nor The Canton Group agreed to speak with Ars about his account.)
In November of 2013, Helkowski said, he was asked by a co-worker on The Canton Group’s team responsible for work with the Drupal Web content management system to help migrate data from a legacy ColdFusion site belonging to the University of Maryland’s School of Public Health. Using the team’s access to the server, Helkowski said he downloaded the contents of the site’s directory from the server to his work computer.
That download set off his malware scanner. Helkowski started to investigate why, and he found that one of the files on the server was a PHP script file. The code in the file had been compressed and obfuscated to hide its purpose, so Helkowski began decompressing and analyzing the code to find out just what it did.
The script turned out to be a piece of Web server malware known as C99Shell—a backdoor script that allows a remote user to execute arbitrary commands on the server, search through the file system, and upload files among other things. Because of the configuration of the server, the remote user was able to execute commands with the permissions of the Web server (httpd) user account. That included access to other University of Maryland websites, which resided in other directories on the same file system. It also came with the ability to change file permissions. “It was pretty close to root access because the user was so widely capable,” Helkowski said.
Based on its creation date in the file system, Helkowski said, the backdoor script had been on the server since 2011—meaning that the server was breached at least once over the last two years. He found another similar script not detected by the malware scanner. It appeared that the scripts were both uploaded to the site through a Web interface that allowed site users to post images to the website. The directory the upload page put files in was configured to allow PHP scripts within it to be executed by the Web server. Not good.
PasswordsAs he was looking at the ColdFusion site itself to figure out how to migrate the university data to Drupal, Helkowski found that ColdFusion was configured with passwords for a host of databases within the University’s network that weren’t directly related to the site itself.
“I made a dump of all the passwords to all the databases in November just to cover my ass,” Helkowski told me. “I didn’t do anything with them, but I wondered why ColdFusion had access to 80 plus databases—I assumed it was secure access and not sensitive stuff. But anything I came across, I made a copy of it and put it in an encrypted container. Just in case something bad happens, I have evidence of what happened.”
At that point, Helkowski said, he took what he learned to a co-worker and then to a Canton Group senior executive.
“I’ve been attempting up until recently to defend The Canton Group,” Helkowski said. “I think what happened was that when we communicated with the [executive], he assumed we communicated to the university, and we assumed that he had, so no one did. I’ve actually said that to other people, that I don’t want to throw them under the bus.”
But Helkowski said that, in February 2014, he learned the backdoors were in fact still on the university server—and they became part of a much bigger problem.
Once again into the breach
This was not a great winter for data security at universities. In March, Indiana University revealed that it accidentally stored the personal data of 146,000 recent and current students on a publicly accessible website for 11 months, and the data was crawled by search engines. The North Dakota University System had a data breach, including SSNs, that began in October of 2013 and continued until early February. And Johns Hopkins University faced a smaller breach, exposing the names and contact information of 1,300 biomedical engineering students. A message from someone claiming to be from Anonymous took credit for the JHU breach:
But the biggest breach of them all would be at the University of Maryland.
Sup fags,
Anonymous here doing nothing but being complete dicks and trolling hundreds of innocent people. You see, recently, we hacked into the “secure” databases of John Hopkins University and acquired roughly 103MB of raw text data detailing the layout and content of their SQL “infrastructure”…Yes. An Ivy League School left their databases open to literally one of the most simple Web application vulnerabilities you can find. If that isn’t reason enough to smack the shit out of them, we don’t know what is.
On February 18, Brian Voss, the university’s vice president of information technology, informed university President Wallace Loh that someone broke into one of those databases Helkowski noticed. The hacker obtained records for 309,079 current and former students, faculty members, and employees. The data included Social Security numbers, dates of birth, and university ID numbers.
In an open letter published the next day, Loh said that “the University of Maryland was the victim of a sophisticated computer security attack that exposed records containing personal information.” Loh apologized and promised immediate action. In a follow-up message, he announced the formation of a computer security task force which would, among other things:
- Conduct a scan of every database to find out where sensitive personal information might be located. Then the task force members will recommend the appropriate course of action: purge the data, or ensure its protection;
UMD President Wallace Loh promises credit protection and better protection of personal data in this video message to students, staff, and faculty on February 25.As news of the breach spread, Helkowski said, he went back to check if the malicious PHP script files were still on the university’s server. They were still there, untouched. Helkowski then decided to check if the attacker could have used the information in the ColdFusion site to gain access to personal data.
“I was like, ‘I wonder if this has access to the Social Security numbers that everyone was complaining about,” he said. “And I said, if they were anywhere, I would bet they were in this database named LDAP.” (LDAP refers to the “Lightweight Directory Access Protocol,” which allows for single login accounts across networked computers and can also provide directory lookups on other users of the network.) As it turned out, the LDAP contained a field labeled “SSN.”
“So I then said, let's query it,” Helkowski said. “And [people on my team] said, ‘No, don't dump that, you shouldn't do that.’” But Helkowski knew someone who was a current student at the university, and he obtained the student’s authorization to check the database for his information.
“So we did a live query [of the database] to pull up his information,” Helkowski said. “And he was able to confirm his Social Security number, date of birth, GPA, major, his student ID number as well as the barcode on the back of the student ID which would actually allow someone to forge student identification cards. That was all in the LDAP database.”
Going rogue
Helkowski began drifting away from being a mere employee, becoming—in his own eyes—a righteous force for good. Determined to get his report into the hands of someone at the university that could act on the problem, Helkowski gave a copy to a student in University of Maryland’s cybersecurity program. He hoped it would be passed on to the University’s security team.
“It was a Wednesday when we discovered [the vulnerability], and it was a Friday when we had a teleconference meeting with UMD, which they did not involve me with at first,” Helkowski told us. “But halfway through, UMD requested me to join to ask me questions and to demonstrate the vulnerability. During the part where they asked me to demonstrate the vulnerability, I said, ‘I can't actively show you a dump of the SSNs because I don't have authority to do so.’ I asked, ‘Do you guys give me authorization to reveal this information, because otherwise I shouldn't be doing this,’ and multiple people on the other end of the line said, ‘Yes, we give you authorization.’”
Helkowski then told them about the database named LDAP.
“They said, ‘We don't know what this is, we don't know where it came from.’ Apparently it's some sort of mirror that someone created for some other application—it wasn't the live directory,” he said. “But I was able to subsequently prove that there was another table that was inside that LDAP database, that was all the user names and passwords that had permission to query that database. That table included clear text passwords for those people as well. And the HTTP user had the ability to see that. In other words, you could write a ColdFusion script, not do any hacking, just hit that database and dump out the main active directory credentials. You could hit that server from anywhere and download that entire directory structure, all 300k of those numbers.”
After finally getting his message across to the university, Helkowski said he waited about two weeks more and checked to see if anyone addressed the problems. The backdoor scripts were archived in place so that they could no longer be executed, and a configuration file (an .htaccess file) had been added to the image upload directory to prevent new scripts loaded there from running. Still, problems remained.
“It was still open access to the database,” Helkowski said. “They did not change any of the passwords. So that’s sort of what triggered me to look further into how bad their security was. Because I was like—if they’re not changing that, they aren’t changing anything.”
Helkowski decided to take his work home with him and see exactly how far he could go in penetrating the University of Maryland’s network. It turned out that breaking into the network from outside was as easy as performing a Google search.
Extra creditHelkowski knew that the backdoor script he reported to the University was closed, but he suspected there might be more exploits in place on other websites within the UMD system that could grant him the same access to university databases.
“I searched for other PHP scripts with the word ‘upload’ in their name by Googling it,” he said. “And then I went and looked at those files, and looked at the code, and they were vulnerable as well. And that’s when I found another shell script. So not only have I found another place that was vulnerable, but it’s already been attacked.”
“They opened my gate to my backyard. They went to my side door and bashed the door in.”Using one of these backdoors, Helkowski didn’t have to do any real hacking to gain access to nearly everything on the server. With the door wide open for him, Helkowski started to see what he could do within the system.
The answer turned out to be just about anything. He managed, using the access made available to him through the Web server’s privileges, to install and compile the Gnu C Compiler (gcc) on the server. He installed the Nmap security scanner on the server. Helkowski even established a remote Xwindow session to the server from his home computer and was able to run Oracle command-line utilities against databases using passwords he was able to read in the script files—including that database called “LDAP.”
“I had access for quite a while. I could have escalated my access,” Helkowski said. “I did not do that but was considering that.”
But Helkowski decided that he reached “the turning point—where I would go from whitehat to black hat,” he said. “I decided I needed to tell them immediately, and I gave them a full list of what I did in detail. That way the university would have full evidence of what I did and be able to distinguish me from a malicious person. I didn't want to interfere with the investigation.”
The way Helkowski chose to communicate that information, however, did not exactly cast him in the best light. He devised a plan that he thought would help both get the university’s attention about the severity of their security problems while keeping him out of hot water. As it turned out, he succeeded on the first count but failed miserably on the second.
Using the LDAP database, Helkowski obtained the e-mail addresses of all of the members of President Loh’s newly formed security task force. He also obtained President Loh’s Social Security number and phone number. On the night of March 14, to demonstrate the seriousness of the situation, he posted the information to Pastebin and linked it on reddit. He then sent a lengthy e-mail to all of the members of the security task force from an anonymous e-mail service, claiming to be a hacker who obtained a copy of the security report that Helkowski leaked to the University.
His e-mail, which was included with the eventual FBI search warrant affidavit, read in full:
“Is there a party at my house?”Security Taskforce,There are current open holes that haven’t been fixed. Out of politeness I’ll give you a chance to respond directly about this to me, and I’ll consider pulling it off the public Internet. Please read
-
 1
1
-
Welcome to our family.
Enjoy! -
Welcome to our family.
Enjoy! -
Welcome to our family.
Enjoy!



I'm back...................
in Introduce Yourself
Posted · Report reply
Welcome to our family.
Enjoy.